Introduction
This article will cover the various authentication methods in the SSH protocol, and how to authenticate an SSH session in LabVIEW using the LabSSH toolkit. A simple VI example will be provided at the end.
The authentication methods to be covered are:
- Plain password authentication
- Public key authentication using a private key file
- Agent-based authentication
- Keyboard-interactive authentication, also known as challenge-response authentication.
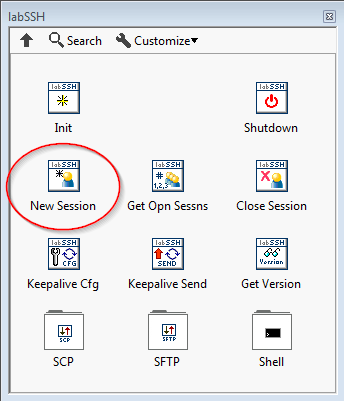
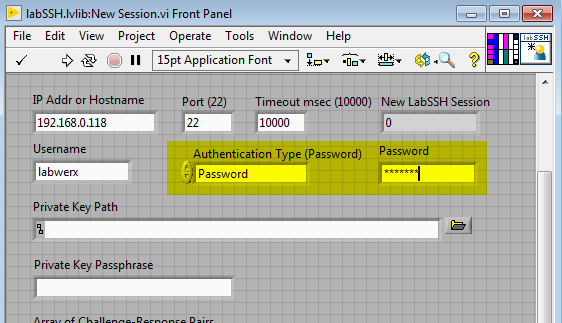
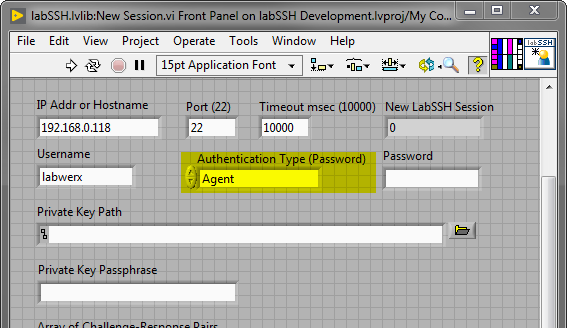
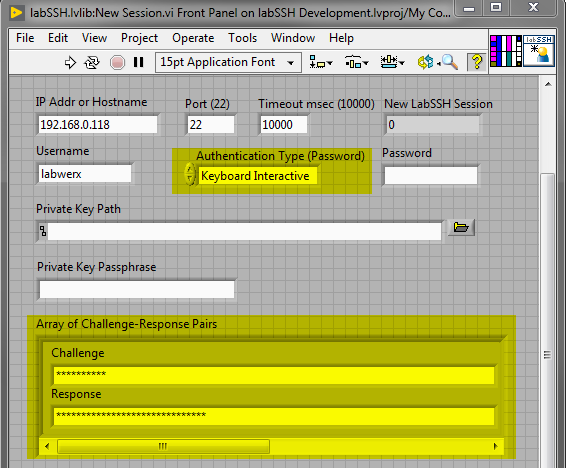
Every example shown in this article pertains to the function New Session.vi, which is solely responsible for SSH authentication within LabSSH.
Password Authentication
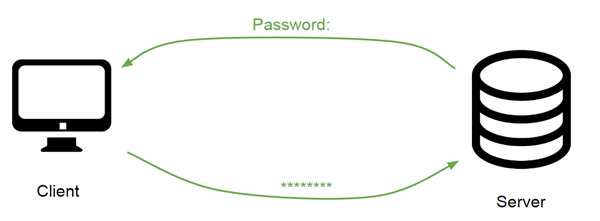
Under the plain-password authentication scheme, the server prompts the client to provide the user account's password.
In the New Session.vi function, you must select the Password option in the Authentication Type choice control, and enter your password in the Password control.
Public Key Authentication From File
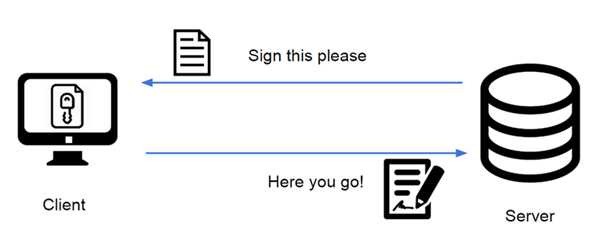
Under public key authentication, the server requires the client to prove its possession of the private key by requesting a unique signature. This signature is verified by the server by checking it against the corresponding public key, which the server has possession of.
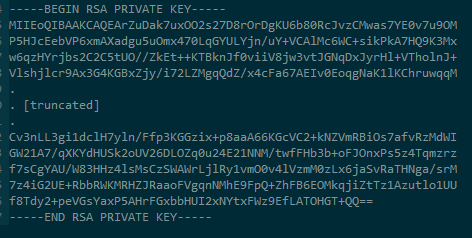
LabSSH accepts private key files in OpenSSH format (PuTTY key files with extension .ppk will not work). Here’s an example of what an OpenSSH key file might look like:
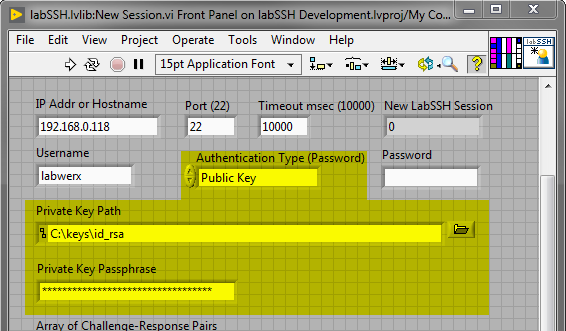
To authenticate using a private key file in LabSSH, select the Public Key option in the Authentication Type choice control, and enter the path to where your private key file is found in the Private Key Path control. Additionally, if your private key is protected by a passphrase, you must enter your passphrase in the Private Key Passphrase control.
Agent-based Authentication
Agent-based authentication is a different form of public key authentication. In agent-based authentication, the public key authentication process is delegated to what's known as an "agent", which is a piece of software running on your system that already has access to your private key files. This agent performs public key authentication as normal.
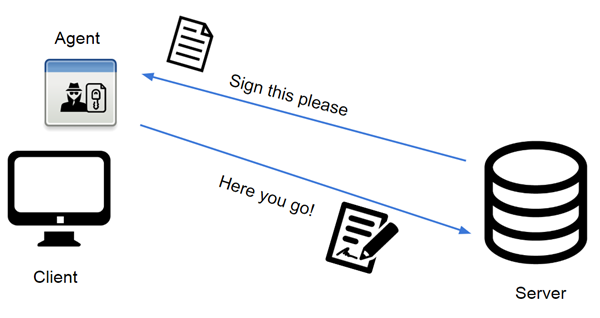
The most common agent is Pageant, which is included with PuTTY.
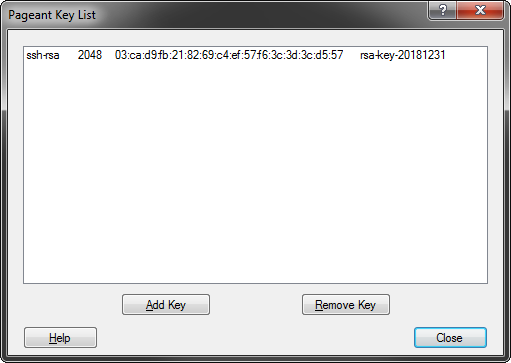
To use agent-based authentication in LabSSH, select the Agent option in the Authentication Type choice control. The private key file path is not necessary, as it is delegated to the agent. It may go without saying, but you should have your agent running and loaded with your private keys before you attempt to authenticate.
Keyboard-Interactive Authentication
Under Keyboard-Interactive authentication )also known as challenge-response authentication), the server issues one or more challenge phrases, each of which requires the correct response from the user.
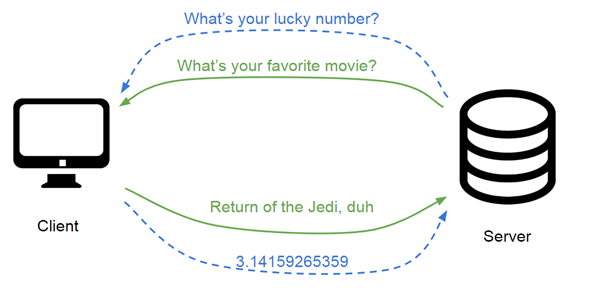
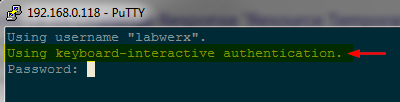
In practice, however, the most common challenge is simply Password: . This is why many new users confuse keyboard-interactive authentication with plain password authentication.
How do you determine whether your server is using keyboard-interactive authentication? Simple. Check to see if your PuTTY window displays the message: “Using keyboard-interactive authentication”. If so, then your server is using keyboard-interactive, and not password authentication.
To authenticate using keyboard-interactive in LabSSH, select the Keyboard Interactive option in the Authentication Type choice control. Additionally, you must enter one or more challenge/response pairs in the Array of Challenge-Response Pairs control.
How LabSSH Matches Challenge-Response Pairs
How does LabSSH use entries in the Array of Challenge-Response Pairs? The Challenge field is a partial string that LabSSH attempts to match to the incoming server challenge. LabSSH performs a substring search to determine which response string to use.
For example, if the server issues the challenge phrase “Please enter your password: “, any of the following strings (placed in the Challenge field) will match this:
- “Please”
- “enter your”
- “password:”
- “pass”
When an incoming challenge string matches a given Challenge string, LabSSH replies to the server with the corresponding Response string.
An Example VI
An example VI is provided which merely attempts to authenticate to your server, then shuts it down and exits. It is saved for LabVIEW 2009 32-bit for easy recompiling to your platform. It depends on LabSSH being present on your system. If you don't have LabSSH, you may download it at the Download page.
Example Authentication VI: ssh-authentication.vi